Technical Briefs
Technical Overview
Cybr IQ, is a patented, and innovative IOT security solution that has tools for traffic monitoring, firewalls for perimeter control, and dashboards for application performance. This overview explores how Zero Trust can be extended to the hardware layer.
The idea is simple: stop trusting devices by what they say they are and start identifying them by what they actually are. By combining hardware fingerprinting, automated discovery, and enforcement tied directly into our existing network infrastructure, the blind spots disappear. Cybr IQ core technology, Electrical Identity Profiling, detects the presence of every device at the physical layer. This allows it to identify spoofed, hidden, or unauthorized hardware even when network data appears normal.
Key Capabilities
Physical-layer discovery that detects devices by
their electrical patterns
Hardware Detection and Response framework to
by
identify and isolate rogue devices
Risk scoring that evaluates every asset's
trust level
Policy enforcement that automatically blocks or alerts
by
on unapproved hardware
Trafficless detection that operates without packet
inspection or intrusive scans
 RoomIQ
RoomIQ
The Blind Spot
- Our tools only see devices when they generate traffic. A silent device can sit unnoticed.
- Spoofing is easy. A NIC can claim to be one vendor when the hardware signature tells another story.
- Manual quarantine is slow. By the time we shut a port down, the damage may already be done.
- Auditors want proof, not promises. Screenshots and config snippets don't cut it anymore.

The Approach
The platform adds four things to our existing stack:
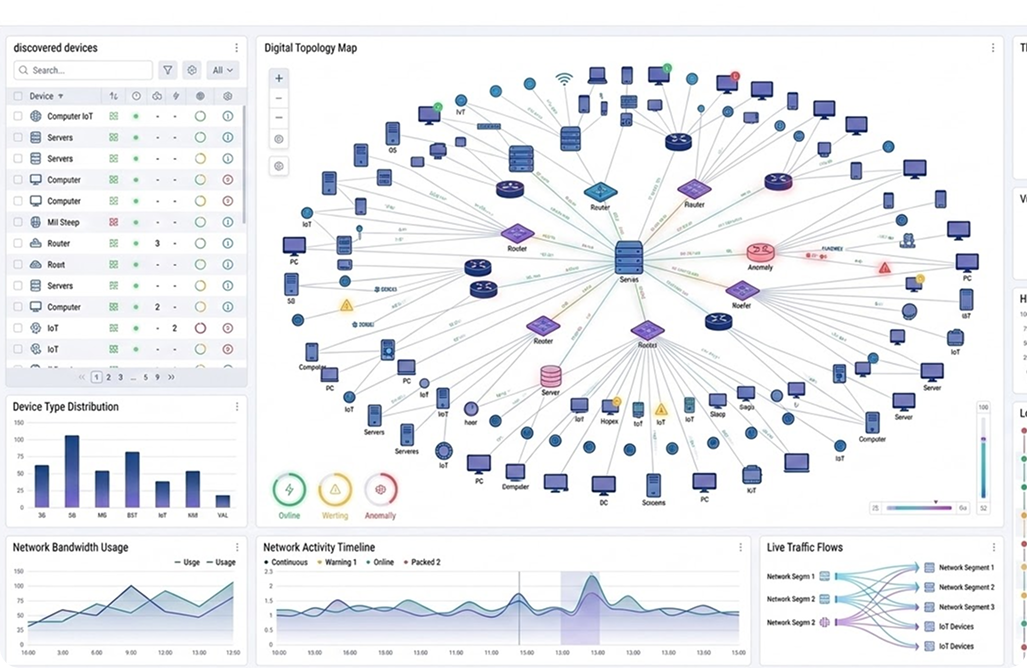
- Hardware Fingerprinting
- Device Discovery
- Policy Engine
- Automated Enforcement
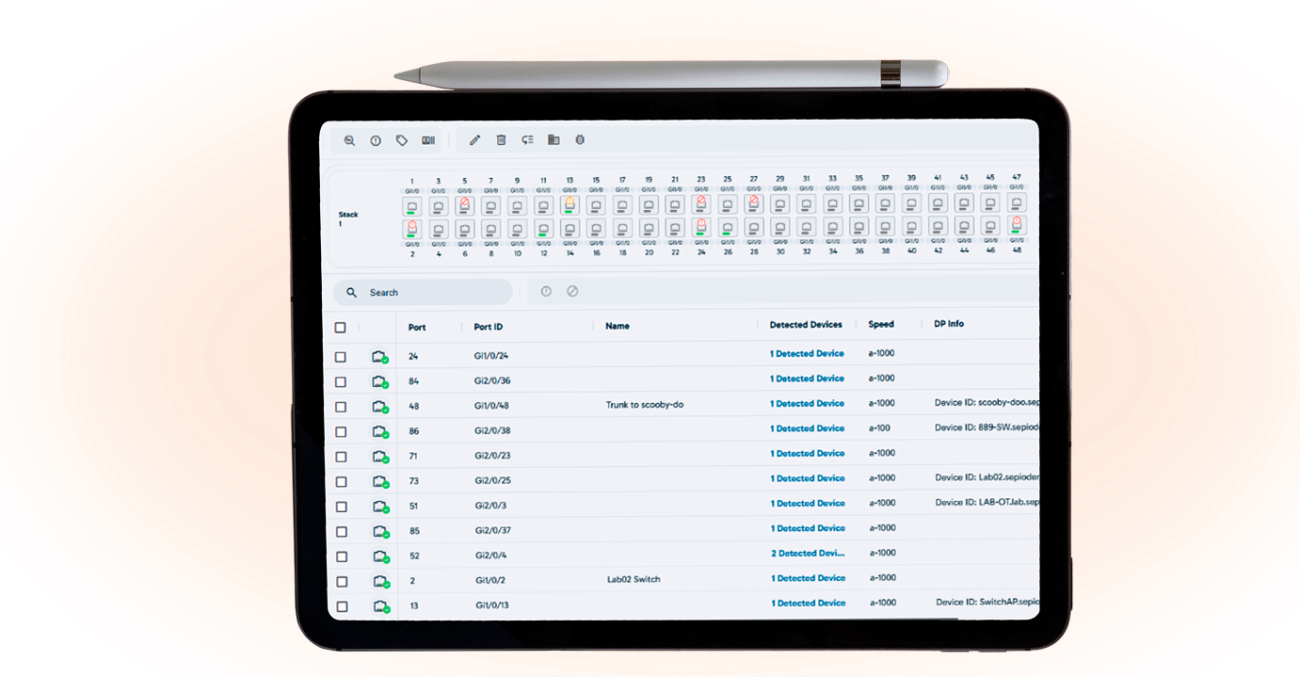
Show Commands
The platform automates the same checks we’ve been running manually for years
- Show interface status
- Show mac addressable
- Show lldp neighbors details
- Show vlan brief
- Show interface transceiver
Instead of manually piecing these together, the system continuously runs discovery and enriches the results with fingerprinting. What once took hours of CLI work now becomes a live, centralized view.

Reporting That Actually Helps
Three reports stand out for network leads:
Device Inventory Report
Complete list of connected devices, each marked as managed, unmanaged, or unknown
Policy Violation Report
Logs each violation, the port, the enforcement action, and the timestamp
Discovery and Enforcement Report
Combines discovery data with enforcement outcomes, proving both visibility and control in a single export.
Device Inventory Report
Complete list of connected devices, each marked as managed, unmanaged, or unknown
Policy Violation Report
Logs each violation, the port, the enforcement action, and the timestamp
Discovery and Enforcement Report
Combines discovery data with enforcement outcomes, proving both visibility and control in a single export.
Device Inventory Report
Complete list of connected devices, each marked as managed, unmanaged, or unknown
Policy Violation Report
Logs each violation, the port, the enforcement action, and the timestamp
Discovery and Enforcement Report
Combines discovery data with enforcement outcomes, proving both visibility and control in a single export.

Reporting That Actually Helps
Making SOC 2 Auditing Easier
SOC 2 isn’t just about having controls in place — it’s about proving them. For network teams, that usually means nights pulling logs, digging through switch configs, and stitching together evidence.
With automated discovery and enforcement:
- Evidence on demand: exports show every device and every policy decision
- Immutable logs: timestamps and enforcement outcomes are preserved for auditors
- Scope reduction: "unknown devices" are discovered, tagged, and either approved or blocked
- Control mapping: policies like "only approved devices connect to production" move from intent to enforced reality.
Technical Overview
Every device on the network discovered and mapped to a switch port.
Fingerprints used to distinguish spoofed from genuine devices.
Violations automatically quarantined or blocked.
SOC 2 auditors handed clean exports instead of piles of screenshots.
Daily review cut to under 15 minutes.

For the network team, this is more than a dashboard. It is seeing everything clearly. Discovery shows what is connected. Enforcement confirms it is protected. Reporting turns compliance into confidence. Zero Trust only works when it reaches every layer, and now it does, all the way down to the hardware.


