Our Solutions
Not all risks look like laptops and servers. Rooms are full of connected gear. Cybr IQ gives
you clear sight and clean control where work actually happens.
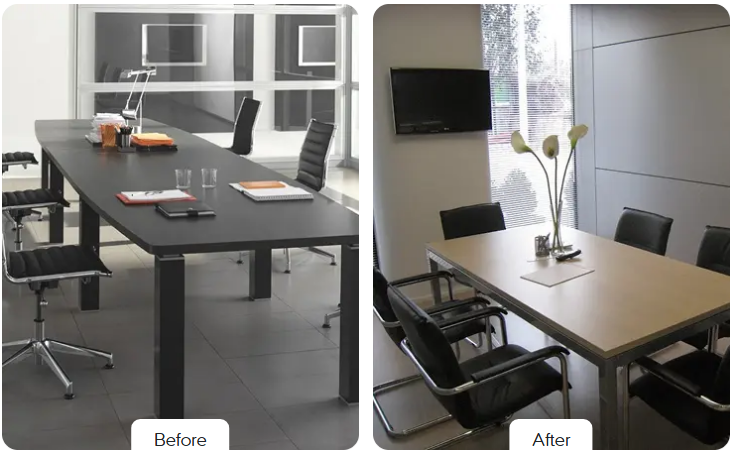
AV / Conference
Room Security
Protect every meeting space. Keep collaboration smooth and secure.
Problem
Rooms collect devices over time. A camera here. A wireless dongle there. A control panel that no one owns. Each one can be a doorway. Most tools ignore them. That creates blind spots and stress for leaders who carry the risk.
Our Approach
- Verify each device before it talks
- Isolate room gear from core systems
- Watch behavior in real time and alert on the unusual
- Apply zero trust so nothing is assumed
Outcomes
- CConfidential conversations stay private
- Lateral movement is stopped early
- Uptime stays high
- Logs and reports are ready for audits

Device Discovery
& Inventory
See every device. Remove every blind spot.
Problem
You cannot protect what you cannot see. Rooms and closets hide gear that never shows up on spreadsheets.
Solution
- Automatic discovery across AV and IoT
- Clear labels by type vendor and version
- Rogue and unknown devices flagged
- One click inventory export for compliance
Benefits
- Clean source of truth for audits
- Faster incident response
- Uptime stays high
- Less time spent chasing surprises

Endpoint Isolation
& Zero Trust
Isolate risk before it spreads.
Problem
Flat networks make it easy for a single weak device to become
many problems.
Solution
- Identity checks for every device
- Micro segmentation for room gear
- Least privilege by default
- Quarantine for suspicious behavior
Benefits
- Smaller blast radius
- Policy that matches modern standards
- Better sleep for your security team

SOC-2 &
Compliance Support
Simplify audits with device level proof.
Problem
Auditors ask for evidence that most teams cannot easily produce for AV gear.
Solution
- Current inventory with ownership
- Continuous logs that show who and when
- Control mapping to trust principles
- Evidence archive that is ready on demand
Benefits
- Faster audits
- Fewer late nights
- Uptime stays high
- Stronger posture for customers and regulators

Threat Monitoring and
Alerts
Detect the unusual before it becomes a breach.
Problem
Traditional feeds ignore AV traffic. Attackers love that.
Solution
- Baselines for normal AV behavior
- Real time alerts on anomalies
- Integrations with your SOC tools
- Short path from alert to action
Benefits
- Faster detection
- Better signal for analysts
- Coverage where tools once had gaps

AI Powered Risk
Analysis
AI that spots what humans miss.
Problem
Thousands of devices and only so many eyes.
Solution
- Learning models that form baselines
- Predictive risk scoring
- Focused recommendations for action
- Dashboards that simplify choices
Benefits
- Less noise and more clarity
- Early warnings
- Faster follow through


