The HIPAA finding showing up over and over in OCR settlements is the same one. The hospital didn't actually know what was on its network.
If you lead information security, privacy, compliance, or IT at a hospital, health system, or large practice group, you have probably noticed that the Office for Civil Rights — the part of HHS that investigates HIPAA — has been quietly closing one resolution agreement after another since the start of 2024. The cited reason is almost always worded the same way: the organization failed to keep an accurate list of the devices and systems that handle electronic patient information. You cannot assess risk on things you do not know are there. Settlements have ranged from about $80,000 to $4.75 million, and most of them come with multi-year corrective action plans that cost more than the settlement itself.
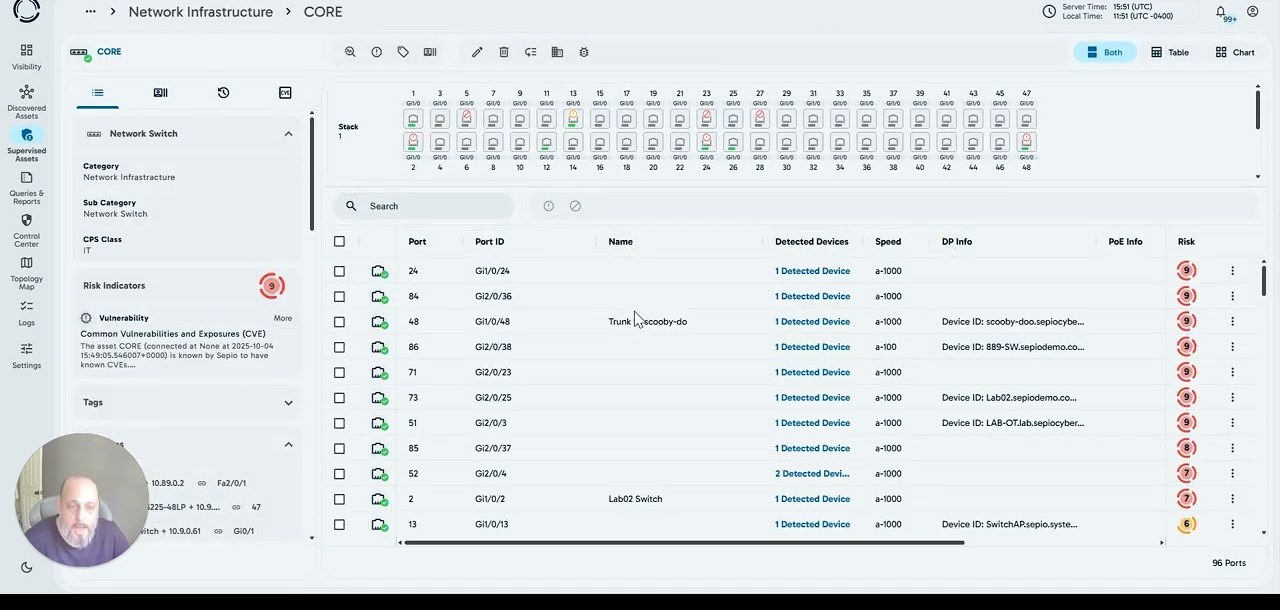
That is the problem CybrIQ is built to close. We connect to your network switches the same read-only way your existing network-management tools already do, and we ask each switch what it knows about the devices plugged into every port. From that information — the kind your switches already collect — we identify each device, including the infusion pumps, telemetry monitors, imaging modalities, pharmacy automation, and the vendor laptops nobody told IT about. We keep that list accurate every day, not once a year for the audit. The list goes into your existing risk register and your existing security tools. We do not look at your network traffic. We do not see patient data. We do not put software on the medical devices. We just keep the list honest.
30-day pilot, no fee. The device inventory we produce during the pilot is yours to keep, regardless of whether you continue with us.
90-second overview. Opens on YouTube.
The four problems we hear about, in plain language.
Different cycles, different stakeholders, same underlying gap: nobody can defend the inventory of what is plugged into the network this morning. We close that gap once, and the four problems below all benefit from the same answer.
The HIPAA risk analysis nobody can prove is accurate.
OCR has been settling cases since 2024 because the asset list underneath the risk analysis was wrong — missing the biomedical VLAN, missing the imaging vendor's service laptop, missing the pharmacy carousel. We surface those devices automatically, with a continuous record that an auditor can verify.
Medical devices nobody can put security software on.
You cannot install endpoint software on an infusion pump or a CT scanner. The vendor contract usually forbids it. We identify these devices from the network side — by looking at how they behave on the wire — without ever touching the device or interrupting clinical care.
USB sticks plugged into clinical workstations.
A radiology tech accepts a USB drive from a vendor to load a study. A construction supervisor plugs something into a wall jack. Some of these are routine. Some are attack tools that look exactly like routine devices. We detect both the unauthorized USB hardware and the rogue network devices that USB tooling creates.
The practice you just acquired, with no documentation.
The asset list is a spreadsheet from 2019. The switch closet has not been audited since the renovation. The new site is already on your network, and the risk analysis you just signed is now wrong. We give you a clean inventory of the new site within hours, in the same format the rest of your portfolio already uses.
What CybrIQ actually does, said the way an auditor would accept it.
CybrIQ is a device-identification platform. We connect to your network switches using the same standard read-only protocols your existing network-management tools already use, and we ask the switches what they know about each port — the manufacturer code on the connected device, how the device announces itself on the wire, the port behavior pattern, and other low-level signals the switch already collects as a matter of course. We never copy or look at the actual traffic running through the network. From the switch-provided information we recognize the device family — an Alaris infusion pump, a GE CARESCAPE telemetry monitor, a Philips PACS workstation, an Omnicell pharmacy carousel, and so on, with about 750 million device fingerprints in our reference library. The output is a continuously refreshed list of every device on your network, in a format your existing risk register, your existing security operations tools, and your existing biomedical inventory system can ingest. The list updates as the network changes. The methodology is documentable. The auditor can verify it.
What CybrIQ will not pretend to do.
We will not tell you we look at whether your devices are configured correctly. We don't — that's a different problem. We will not tell you we "detect threats in real time." We don't — we identify devices and notice changes; the threat-decision lives with your security team and your other tools. We will not tell you we put software on infusion pumps or imaging modalities. We don't — and we couldn't, even if we wanted to. The shorter list of what we actually do is the more useful one for a HIPAA risk analysis: we tell you, with confidence, what is on your network right now.
The frameworks our output slots into.
A defensible device inventory is the first thing every major healthcare cybersecurity framework asks for. We supply the inventory once, and the rest of your program reads from it.
The HIPAA Security Rule — specifically §164.308(a)(1)(ii)(A).
This is the section of HIPAA that requires every covered entity and business associate to conduct "an accurate and thorough" risk analysis of the systems holding electronic protected health information. The single word doing the heaviest lifting in that sentence is accurate. An inventory missing the radiology VLAN or the pharmacy carousel is, by definition, not accurate. That is the gap our output fills.
HHS 405(d) Health Industry Cybersecurity Practices (HICP), 2023 Edition.
HICP is the HHS-recommended cybersecurity framework for healthcare. It comes in two versions: a Technical Volume for small organizations and a Technical Volume for medium and large. Both list "device identification" as a prerequisite to nearly every other Practice in the document. We provide that identification step. Following HICP also gives you mitigation credit if OCR investigates you, under the Public Law 116-321 amendments to the HITECH Act.
HSCC HIC-MaLTS — guidance on legacy medical devices.
The Health Sector Coordinating Council publishes guidance the field actually reads. HIC-MaLTS is the title's shorthand for "Managing Legacy Technology Security." It is the document that says, in plain language, that legacy medical devices will keep being used past vendor end-of-life and that you, the health delivery organization, own the compensating controls. The first compensating control on every checklist is identification. We supply it.
HHS HPH Cybersecurity Performance Goals (CPGs).
The CPGs are a voluntary baseline HHS published for the healthcare and public-health sector. They have two tiers — Essential and Enhanced — and they are increasingly being written into contracts between health systems and their business associates. Both tiers open with asset inventory. We supply the same inventory regardless of which tier you are working toward this year.
A live walk-through of the platform, and a real conversation about whether it would fit your environment.
No slides. No pressure. Bring the questions your last audit raised, the devices Clinical Engineering and IT still argue about, or the practice you're about to absorb. We answer in your context.
Book a demo30-day pilot, no fee. BAA available. Telemetry stays in your chosen region (U.S., EU, Canada, or fully on-prem).
