In one sentence: CybrIQ watches the network, identifies every device connected to it, and tells you (and your evidence pack) the moment anything changes.
This page is the plain-language version, written for the Director conversation with your CEO, CFO, board, or non-technical procurement reviewer. The goal is to make the product easy to describe in your own words, without engineering jargon you'd have to translate. The technical underpinning is summarized at the end of the page if you want it.
90-second overview. Opens in a new tab on YouTube.
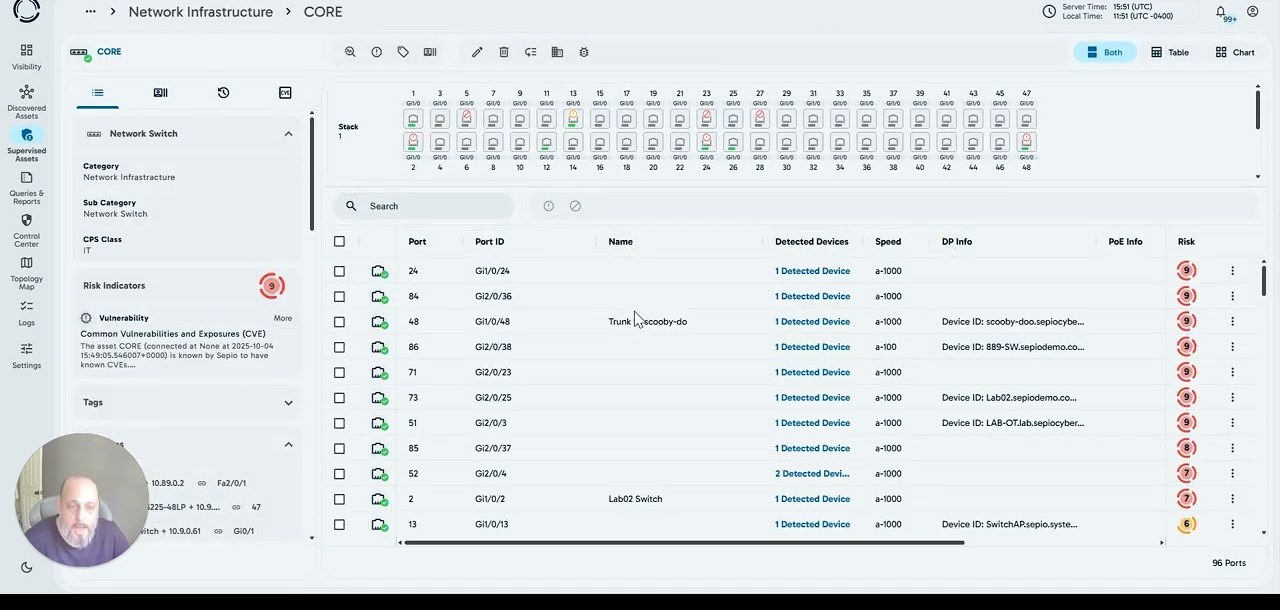
What you see when you open the platform.
Click each hotspot (or use the prev/next buttons) to step through what the platform actually shows when it lands on your environment. The screenshot is sample data; the structure is what your environment populates.

The three things it produces.
Everything CybrIQ delivers comes out of one continuous data stream. Three exports are pre-built; the rest is queryable.
One data stream in, three exports out, three audiences served.
1. A live inventory of every device on your network.
Workstations, servers, switches, conference-room AV, biomedical equipment, plant-floor sensors, IP cameras, IoT devices, printers. Anything connected to a managed switch on your network. Each device tagged with vendor, model, first-seen, last-seen, and the framework controls it satisfies.
2. A change log, continuous, that captures every add, remove, and modification.
Every event timestamped, attributed where attribution is possible (which switch, which port, what changed), cross-referenced against your change-management system if you connect it. Approved changes auto-resolve; unexpected changes route to your security team.
3. An evidence pack, mapped to your active compliance frameworks.
The continuous inventory and the change log, formatted into the artifact your auditor, your insurance carrier, and your board want. Cover-sheet per framework, control mapping per row, signed at the control plane so the integrity is verifiable.
How it gets the data, in non-engineering language.
It asks the switches.
CybrIQ runs a small piece of software on a server in your environment. That software talks to your managed switches (Arista, Aruba, Cisco, HP, Huawei, Juniper, Meraki, Rockwell Automation, Ruijie Networks) using read-only queries every 30 seconds. The switches see every device that connects to them. CybrIQ asks the switches what they're seeing, then assembles the picture.
What this means in practice: no agents on the devices being inventoried. No tap or mirror-port hardware to install. No probing or scanning that could alarm the operators of sensitive equipment. The switches are the source of truth; we read from them.
It tells the difference between devices that look alike.
Two devices with the same MAC address, same model number, same network response patterns can still be different physical devices. CybrIQ uses signals the switch supplies about each device (the kind of signals an attacker can't fake from the device side) to tell the real device from a clone, an emulated device, or a swap-out. From a Director's perspective, this is the answer to "how do you know the device hasn't been swapped?".
It checks against a reference database for known-good and known-bad device fingerprints.
The signature derived from each device is checked against a reference database of 750M+ known device fingerprints, curated and refreshed twice weekly with human review. That's how CybrIQ can tell you "this is a Cisco IP phone, model 7945, manufactured 2019" vs. "this is a banned-vendor IP camera that procurement records say is a different brand." The reference database is the curated knowledge that makes the raw fingerprint useful.
Who consumes the output.
Your security team consumes the live event stream: drift events route into your SIEM via syslog or REST API, the same way EDR and NDR events arrive. Your audit team consumes the evidence-pack exports on the audit cycle; same artifact, different cover sheet per framework. You, the Director, consume the board-ready exports quarterly: inventory completeness, drift trend, framework readiness, notable events. Your insurance broker consumes the renewal-questionnaire artifacts annually: inventory, drift report, sanctioned-vendor screening. Your CFO doesn't consume CybrIQ directly; what they see is the labor-and-consultant savings flowing through the operating budget.
What changes when it's running.
Three things change in the first 90 days. The inventory question stops being a quarterly project. You stop reconciling spreadsheets and start querying a live system. Compliance evidence stops being a renewal-week sprint. The artifact is current; you filter it for the auditor's cover sheet and you're done. The board conversation shifts. You walk into the quarterly update with numbers from a tool, not a spreadsheet your team built the night before. The downstream effects (better insurance posture, cleaner audit cycles, less consultant spend) compound over the second and third years.
For the Director who wants to defend the technical claim without becoming the engineer: CybrIQ derives a SHA-256 deterministic signature from a set of switch-supplied signals about each connected device. The signature is checked against a 750M+ reference database, curated and refreshed twice weekly with human review. Output flows over RFC 5424 syslog and a REST API into your existing SIEM. The technique is mapped to MITRE ATT&CK where applicable (T1200 hardware additions, T1078 valid accounts in the spoof-resistance case). The threat model documents trust boundaries explicitly, including what the platform deliberately doesn't see. Briefing covers the engineering questions in depth if your senior engineer wants to attend.
See the platform, against an environment that resembles yours.
A live demo of the platform against a representative environment. Then a conversation about whether CybrIQ fits your organization. No slides.
Book a demo